Update 26.1.2021: Almost immediately after posting this I got a comment that “adhoc tenants” are being replaced in March with “one time passcode”. I have to say, thanks, finally!
https://redmondmag.com/articles/2021/01/05/one-time-azure-passcode.aspx
In this post I’m trying explain you the following situation:
I’m an enterprise Teams admin and I want to see the end user experience of a user that is being invited as a guest to my Teams tenant. I have a private Outlook account that has been enhanced with Office 365 Home subscription and a custom domain.
What happens and why? How to revert the changes once you’re ready?
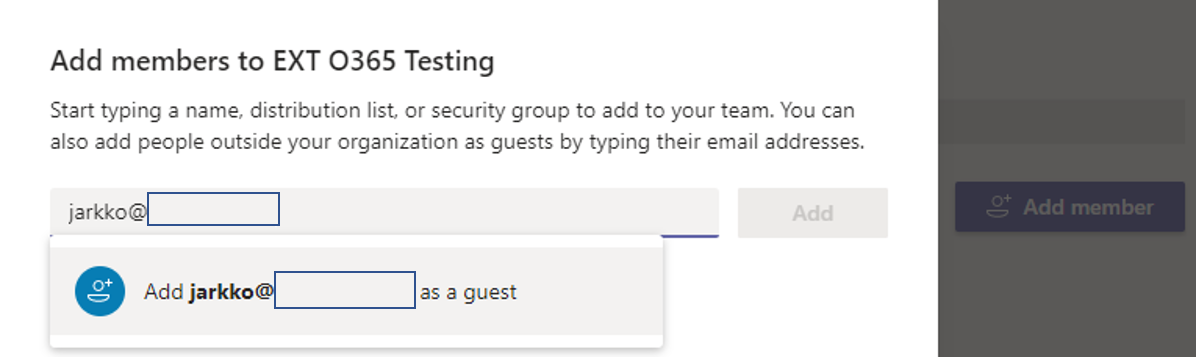
- Adding my private email as a guest user to the enterprise teams
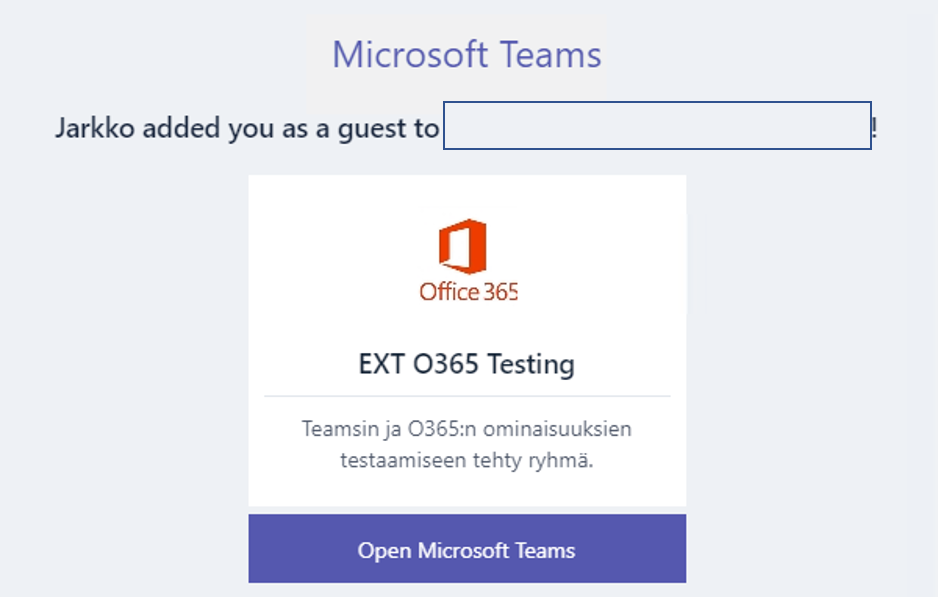
- I’m getting the invitation email as expected
- The guest user gets created to my enterprise AzureAD

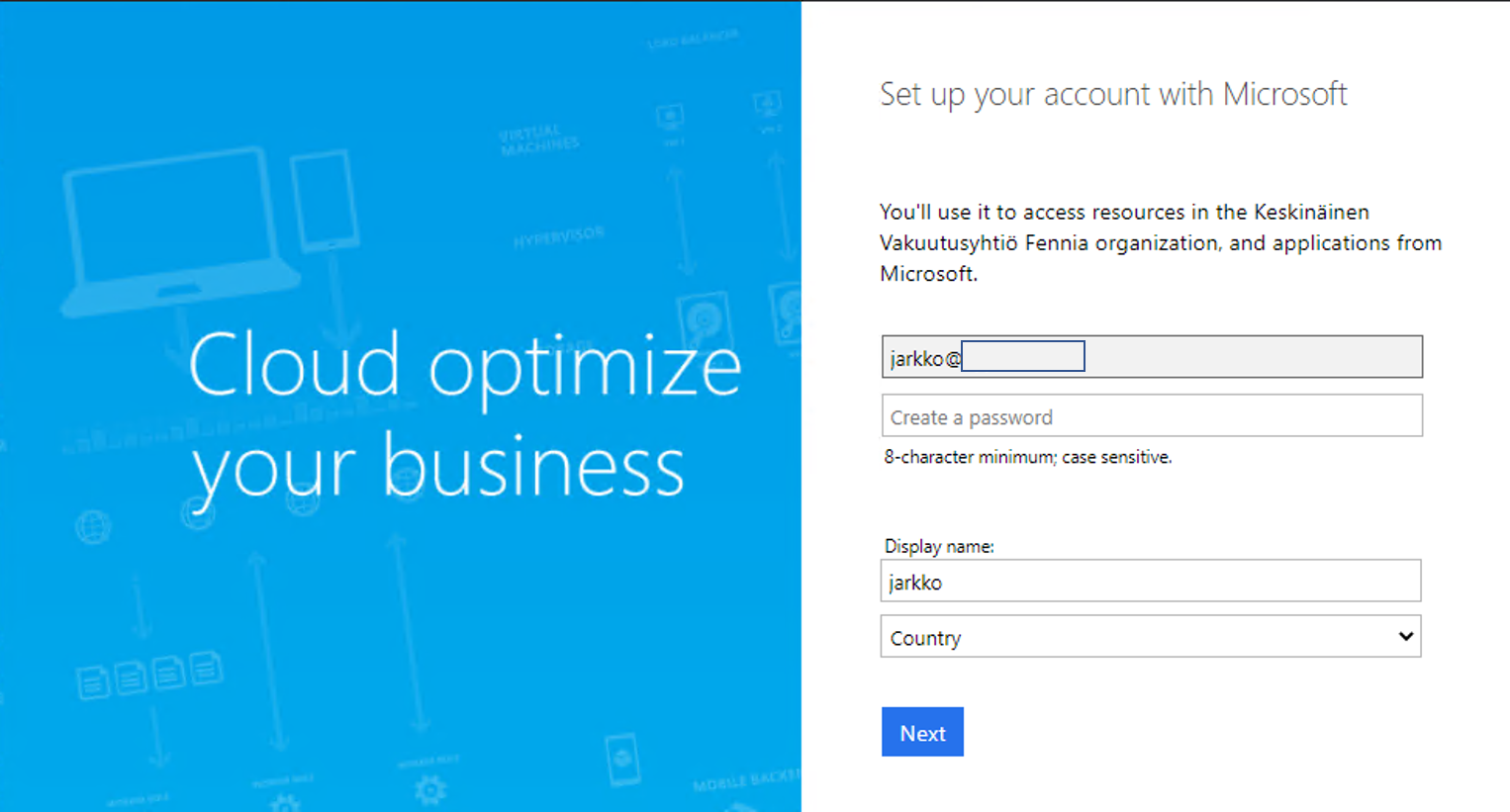
- Clicking the invitation link I’m prompted to set up an account. This is because my email address had only a personal Microsoft account attached to it
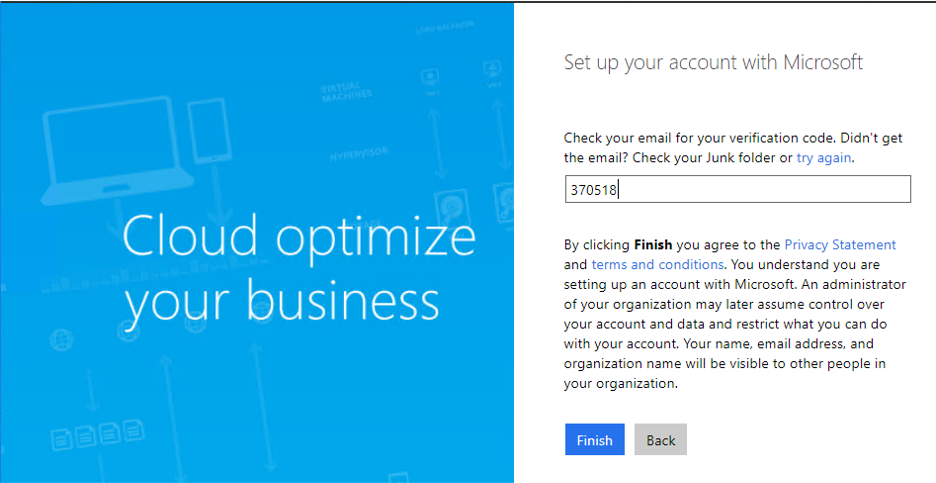
- I’m also prompted for a pin code to verify that I have access to the specified email
- Next prompt asks to give certain permissions for the inviting AzureAD tenant. After accepting this one the invitation process is finished

- This is when unwanted things start to happen. Now both my private Microsoft account and this new account created for the Teams guest usage use the same email address. Because of this Microsoft is going to have issues figuring out which one I’m trying to use. For my personal account this broke passwordless functionality, Outlook and caused login issues including this annoying popup every time

- While accepting the guest invitation a new AzureAD tenant was created in the background

- One might think that removing the guest user from enterprise AzureAD would help

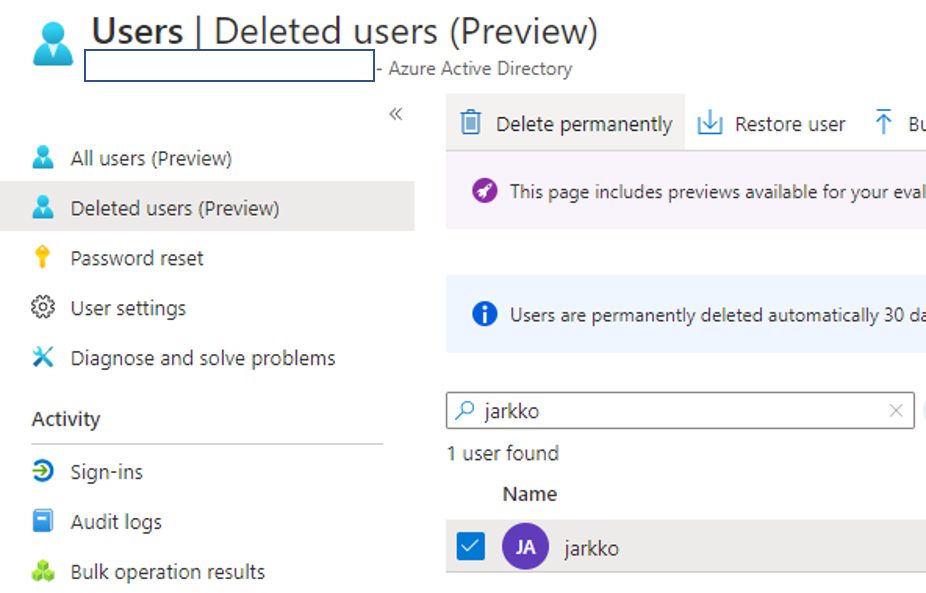
- … and when it didn’t help, maybe permanent deletion does? No luck with this one either. It is important to understand that the guest account in the inviting AzureAD is basically only a reference (actually it has some local attributes also) to another directory. No changes are written in any direction after accepting the invitation (at which time the user name etc. gets copied from invited directory). So changing or removing the guest account makes no difference to the other side. This is why my email address still has two accounts tied to it and the problem remains.
- Looking at the newly created AzureAD (created by the guest invitation) we can see that my account is still there. I actually logged in to the https://portal.azure.com portal with that account created in the step 4

- That user account has only “user” permissions to that AzureAD tenant so we need to do some more steps to solve this problem. We can begin by logging in to the https://office.com portal
- From the left navigation we can select the “admin” view
- This redirects us to https://admin.microsoft.com/admintakeover

- I need to verify that I own the domain. This is done by adding a TXT record to the domain DNS

- Verification can be done almost immediately. After doing this my account gets Global Administrator permissions

- Then its good time to read from https://docs.microsoft.com/en-us/azure/active-directory/enterprise-users/directory-delete-howto what is needed to delete this AzureAD tenant. First requirement is using external account. So I’m inviting a guest for this purpose

- Then I need to add Global Administrator permissions for this invited account. This can be done in the https://admin.microsoft.com portal

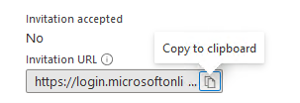
- Before being able to administrate this AzureAD with the invited account, you must first accept the invitation. In case you don’t have access to the mailbox of that user account you can acquire the invite link from the https://portal.azure.com portal

- After selecting “Resend Invitation” you are provided with a option to copy the invitation URL
- Then you can login to the https://portal.azure.com. Remember to switch to the directory that you plan to delete
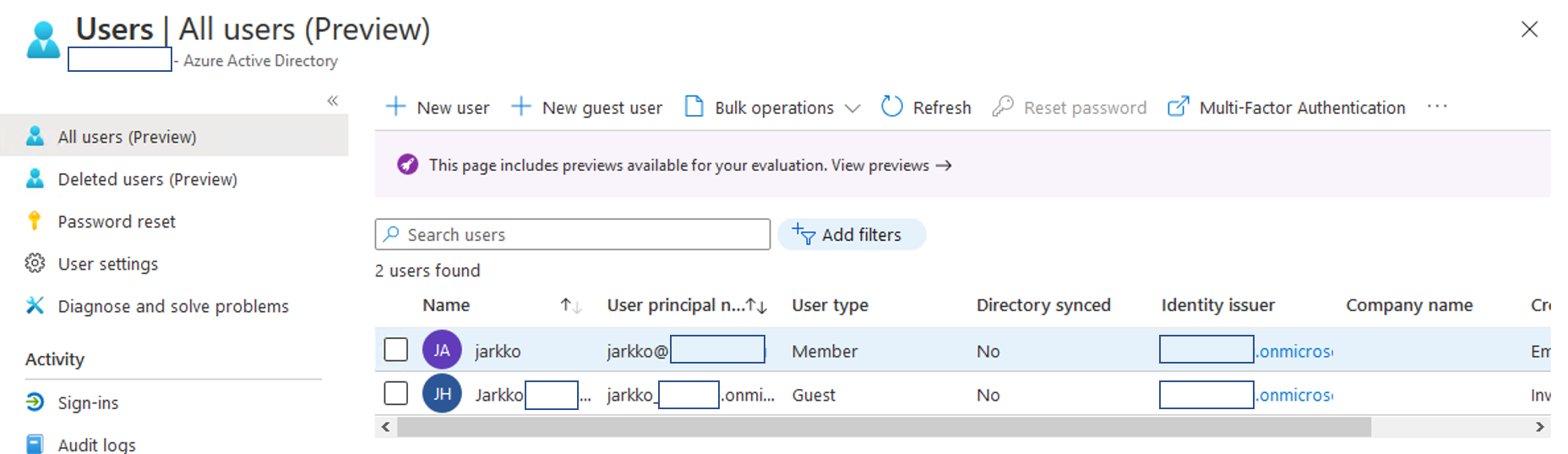
- Next step is removing all local accounts from this AzureAD. This time it means the only one that was created by step 4
- Then we can return to AzureAD “Overview” and select “Delete tenant”

- The wizard is easy to follow. It gives some steps to fix before going further
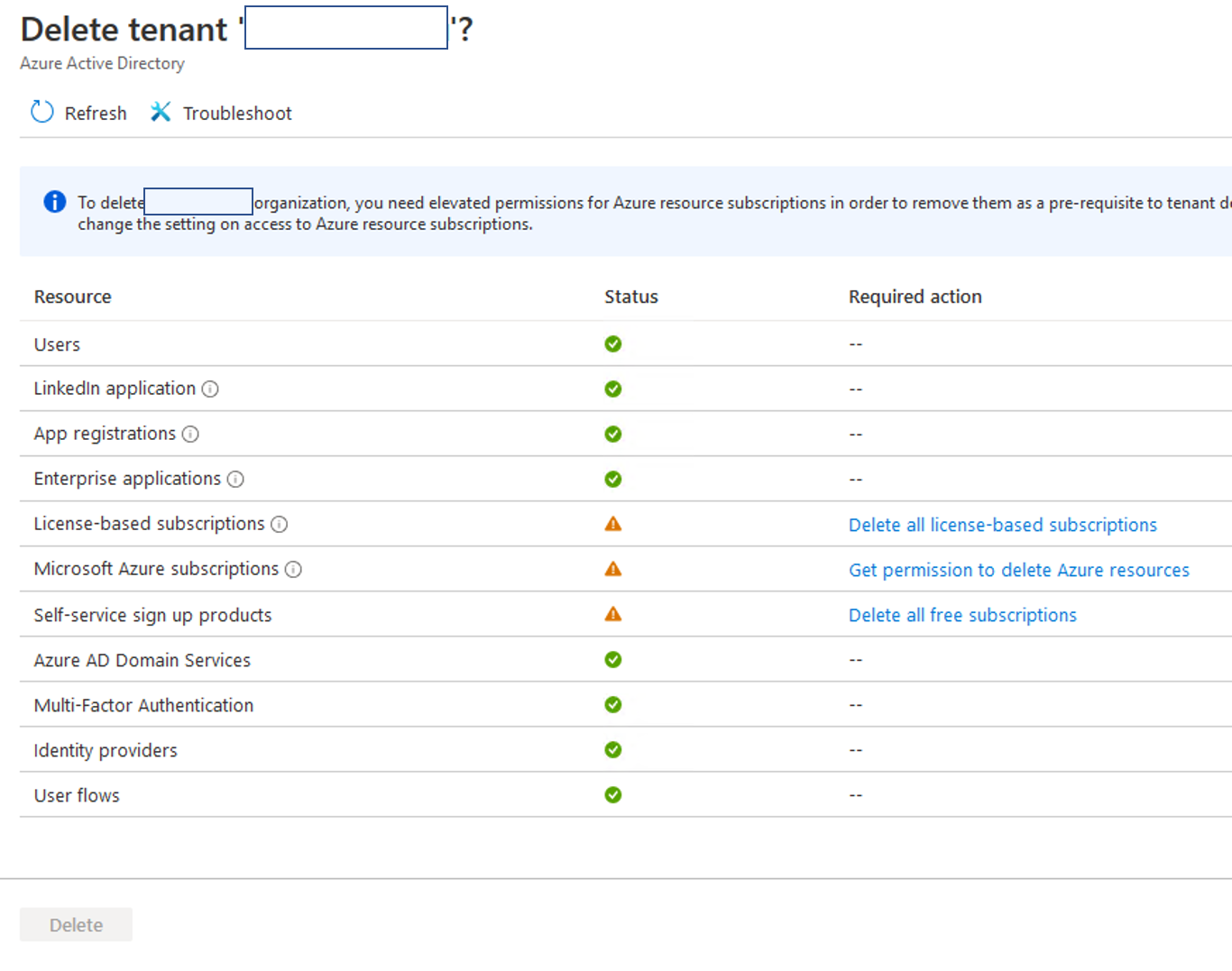
- I’m going to select “Get permission to delete Azure resources” first. This actually only adds full permissions to all Azure subscriptions connected to this AzureAD tenant. This time it only verifies that I have no Azure subscriptions present

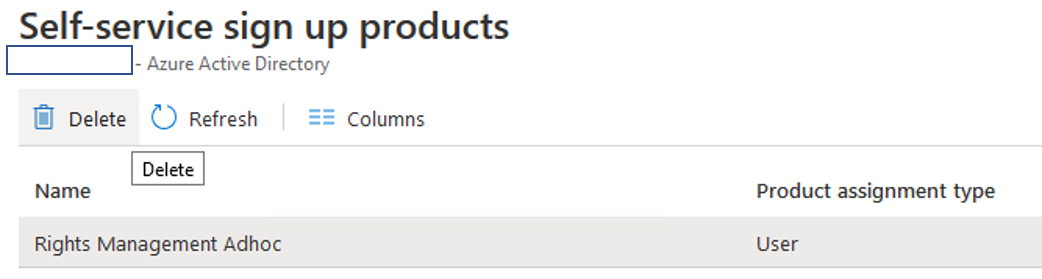
- Then I’m selecting “Delete all free subscriptions”. This refers to licenses. “Rights Management Adhoc” subscription had been automatically added so it must be removed at this stage
- Finally we are ready to remove this AzureAD tenant to cleanup the rest of this experiment

- All done. Finally my private email address has only one account attached to it. No more prompts for selecting which one I want to use. Also Outlook and authentication started to work again as expected

This was a good exercise for me to understand better this one kind of use case. The only worry I have is with the fact that some other might encounter this also and what if that poor human doesn’t happen to be an IT professional? There is nothing that inviting party would be able to fix. I tried to ask for instructions from Microsoft myself with no luck. Office 365 Home and custom domains are targeted to consumers, so this unfortunate scenario might happen to some else as well.
