Like for many other cloud services also Azure has a huge bunch of promises, rapid deployment of services and flexible pricing to mention a few of those. One thing in common for this kind of native cloud services is a “built from zero” attitude. Microsoft has been involved in identity governance for a long with their “Identity Manager”. With this long background I think they should have been ready faster with identity governance offerings for the cloud (and hybrid of course)!
I must admit that I missed Ignite 2018 and the presentations regarding AzureAD Entitlement Management. Until this feature came to public preview a couple of weeks ago I had already lost hope on Azure’s capabilities on this side. To make things even worse Azure has a quite powerful B2B model with its guest user approach. This easily leads to a new type of users with no life cycle management. I was aware of Access Reviews functionality but being bundled to Azure AD P2 licensing its not applicable for all cases. This all left me playing around with ideas on what I could do with “Microsoft Identity Manager” connected to AzureAD.
I first encountered Forefront Identity Manager roughly 10 years ago. After that I have been involved with identity management and Microsoft Identity Manager every now and then. For the last 18 months its been my professional main focus. I attended Oxford Computer Group’s Microrosft Identity Managed Advnaced course last year. The instructor told that if someone asks “can you do it with MIM” – the answer is always “yes”, but it ain’t always wise to do so. With this inspiration I have taken the challenge with a couple of “can you do it” opportunities.
The rest of this post will present a couple of use cases that I have came up with. The setup I’m using for the demonstration is built for this case only and thus I have only implemented required parts to demonstrate my ideas. I will not make any comments on licensing and this setup is not thoroughly tested or ready for production.
This blog post is accompanied with a Youtube video demonstrating the use cases discussed here. I think It will show some beauty, so I recommend watching it, if you have read this far.
Demonstration setup
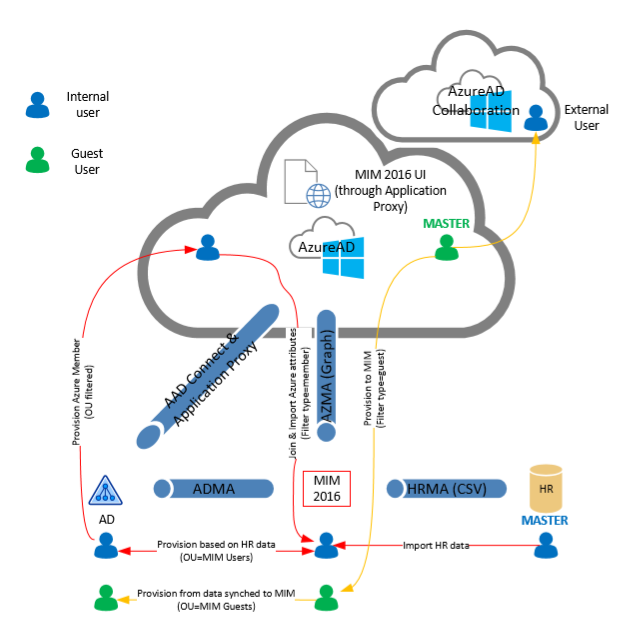
The following picture shows my setup. I have a couple of AzureAD tenants (primarily for playing with B2B functionality), on-premise Active Directory, Azure AD Connect and of course Identity Manager (MIM 2016). I also prepared to use CSV based HR source but for the following examples it won’t be used.
Use cases
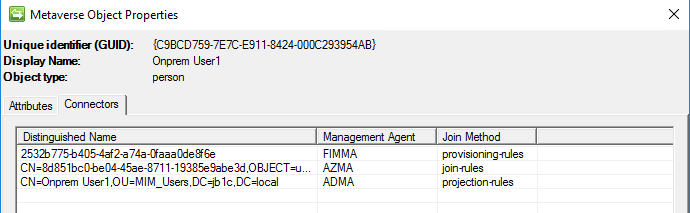
Joining AD and AzureAD objects in MIM
Create user in on-premise directory, let AAD Connect synchronize it to Azure AD and then join both on-premise Active Directory and Azure AD objects to the same identity in Identity Manager. I see this useful in case you want to do something with Azure AD groups in Identity Manager. In this demo I will show these groups and their members in Identity Manager to achieve single point of view to identities and their permission regardless if they exists in om-premise, cloud or hybrid setups. This can be of course extended with what ever processes you might have already available. Maybe you want to detect when Azure AD user is no longer a member of any groups and launch the leaver process for such a user?
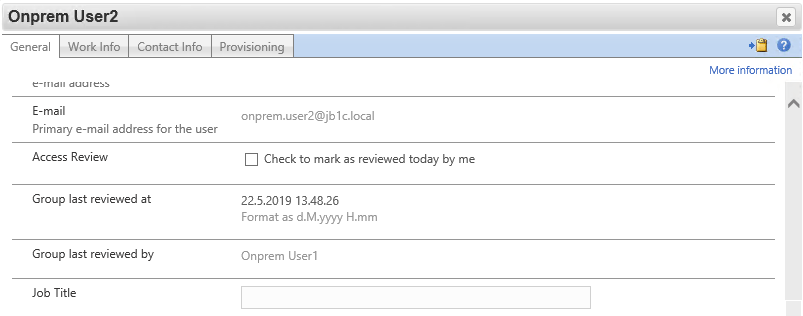
Access review
Apply access reviews for both users and groups. I will demonstrate a light weight process for access reviews with Identity Manager. These can be extended as well. Maybe trigger a review process for users based on a change on manager attribute?
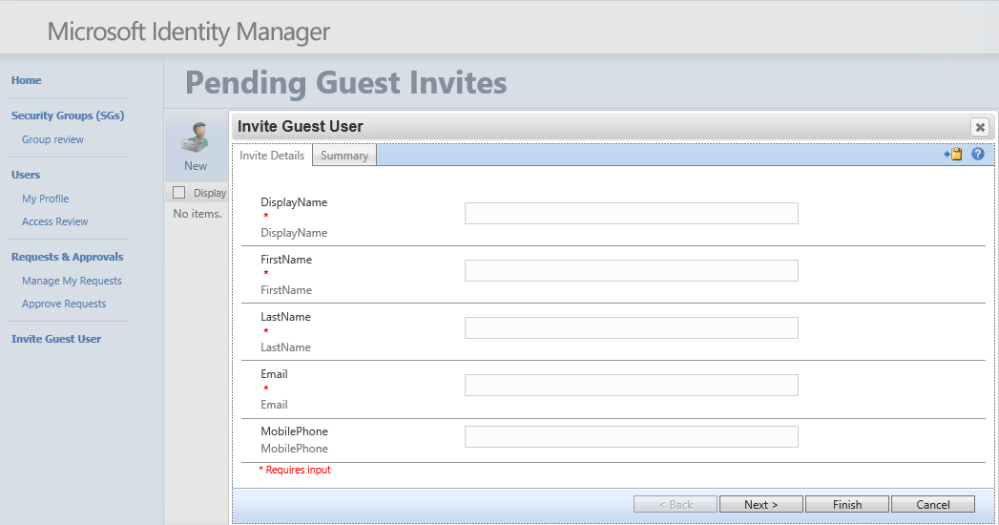
B2B guest invites (with MFA from the first login)
This customization might be useful if you want to use some already existent granularity for allowing invites or if you want to do a little bit more than what’s available with out of the box invite functionality in Azure. This demo will include setting a couple of parameters (givenname,surname,mobile) and sending a customized invite message. With this approach you can achieve Multi Factor Authentication from the first login if you also set strong authentication methods through MSOLService powershell together with preset mobile phone number.
In the background powershell will send the invitation:
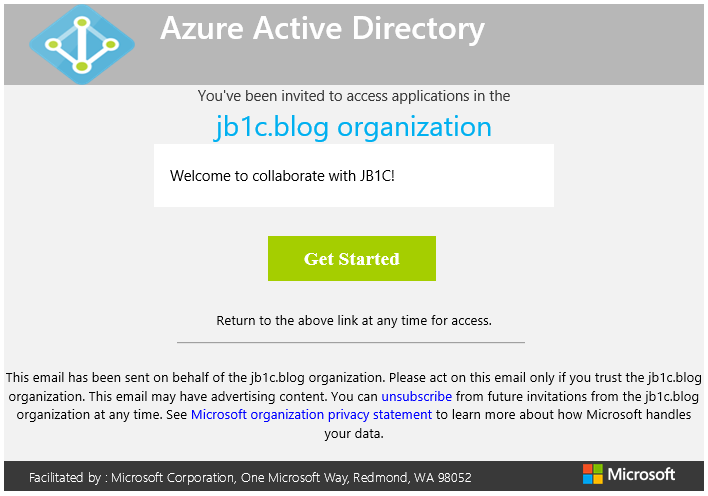
With my custom invite process, when the user logs in for the first time, you won’t get this:

But instead you will get this:

I think that’s a really huge difference. Any of invited accounts can access your application directly (e.g. login.myapp.com) even without an invitation link which leaves a moment without MFA protection. You might have thousands of invited users, who haven’t accepted the invitation, and for those accounts there is no true MFA with the standard invite process.
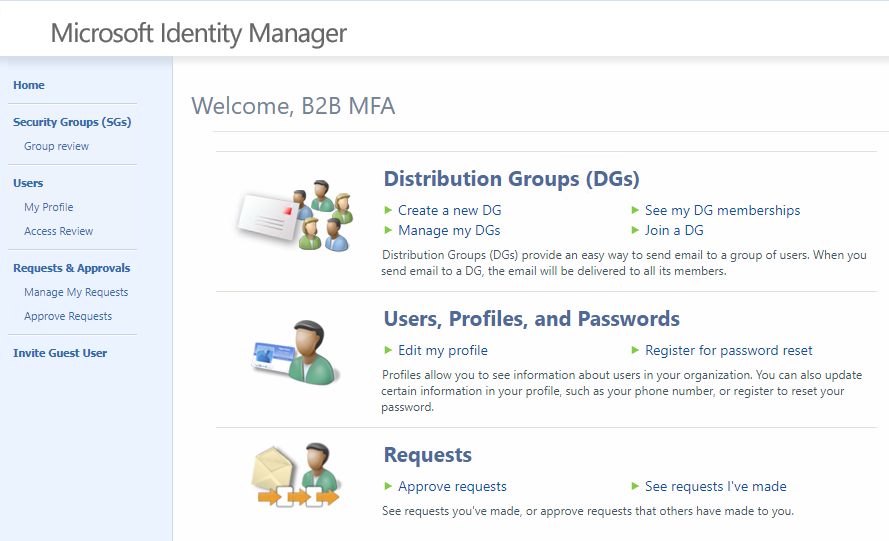
Self service functionality (for all users)
The interesting part here is the self service for AzureAD based users. This works regardless if the users are “members” created in your AzureAD tenant or “guests” invited from elsewhere.
Final words
Good old MIM 2016 is usable for the above cases pretty well. One could of course hope for a modern UI and easily accessible APIs. Hopefully we will get more functionalities to Azure or at least updates to MIM. I did intentionally keep this post away from details about my configuration. If there is something specific that interests you, please leave me a comment or message. I’m happy to share more details later if that’s useful for someone! Below I have left some references for instructions and components I have been using for this demonstration.
This content was brought to you “Just Because I Can”!
References
Microsoft Identity Manager Deployment Guide: https://docs.microsoft.com/en-us/microsoft-identity-manager/microsoft-identity-manager-deploy
Microsft Identity Manager Graph Connector: https://docs.microsoft.com/en-us/microsoft-identity-manager/microsoft-identity-manager-2016-connector-graph
Azure B2B with MIM using Azure Application Proxy: https://docs.microsoft.com/en-us/microsoft-identity-manager/microsoft-identity-manager-2016-graph-b2b-scenario
Lithnet AutoSync: https://github.com/lithnet/miis-autosync
MIMWAL: https://github.com/microsoft/MIMWAL
AzureAD Entitlements Management: https://docs.microsoft.com/fi-fi/azure/active-directory/governance/entitlement-management-overview